Hakeem Anwar: AI Expansion, Surveillance, and Control [Full Interview]
Exposing the technological developments which are reshaping behaviour, straining the environment, and eroding autonomy
Introduction
This conversation with Hakeem Anwar explores the accelerating convergence of artificial intelligence, resource extraction, and surveillance systems, and how these forces are reshaping both the physical and digital landscape. From the hidden environmental costs of massive data centres to the quiet expansion of digital ID systems and the normalization of surveillance in schools, a consistent pattern is emerging. Infrastructure is being built not just to serve technology, but to reorganize human behavior around it.
Save up to $150 on private phones and laptops
In an era of digital surveillance, algorithmic bias, and growing censorship, privacy has never been more important. As centralized powers extend into every layer of our digital lives, those who value truth, freedom, and autonomy need tools they can trust. Above Phone delivers exactly that, and my core team relies on Above Phones and Above Books to run our operations securely.
Save up to $150 on privacy-focused devices—including laptops, tablets, and phones—while supporting the educational and advocacy work of my team, Take Back Our Tech, and Above. Use discount code DRTROZZI or access the offer through the link below.
This interview with Hakeem Anwar is rich with insights, but we know time is limited. Below is a concise summary highlighting the key takeaways from our discussion for your convenience.
The Rise of Data Centres and their Cost
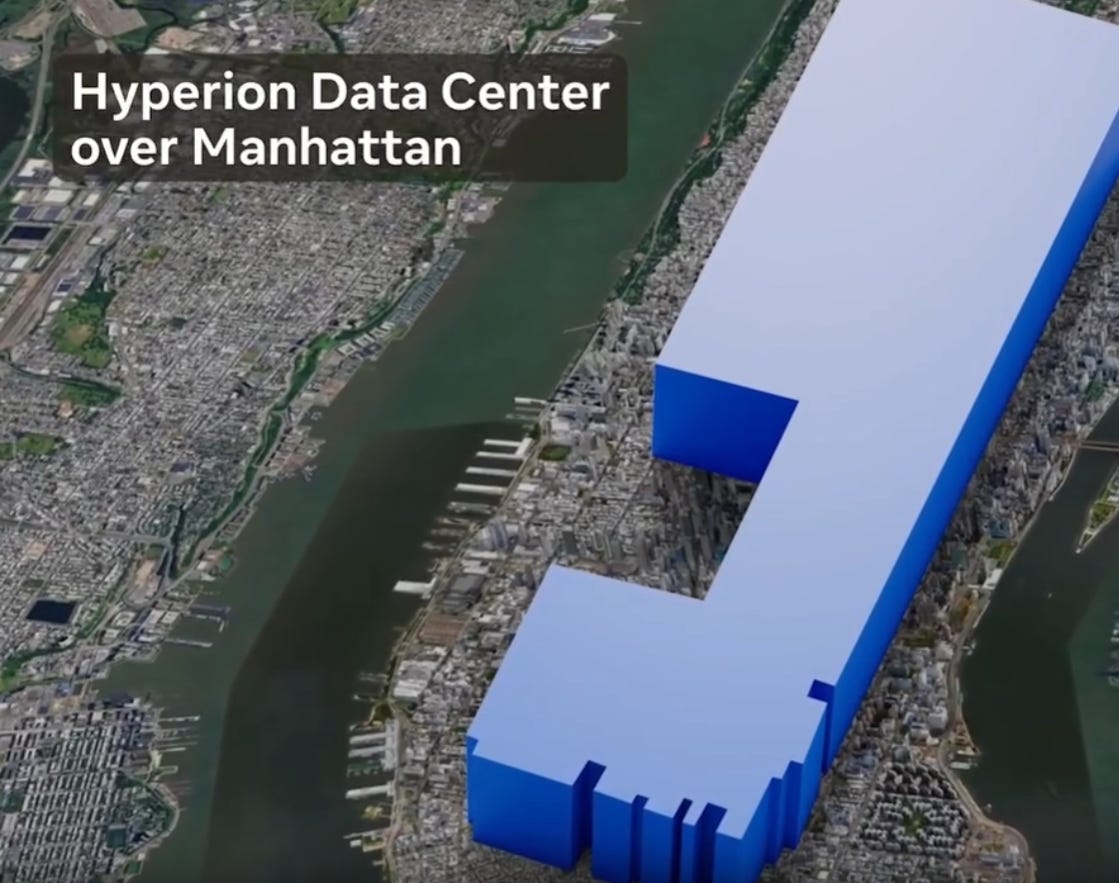
At the core of the modern technological push lies a resource-heavy infrastructure: data centres. Through his independently developed data centre mapping project, Anwar identified thousands of facilities across the United States, revealing dense clusters near major cities. The visualization, built from both public and private datasets, highlights just how rapidly this infrastructure is expanding.
What distinguishes the current wave is not just scale, but intensity. He points to individual facilities, such as Meta’s Hyperion project, which approaches the size of Manhattan and is projected to consume massive amounts of electricity and water daily. Estimates derived from publicly available energy and water usage models suggest that even a single large data centre can place meaningful strain on local resources.
The implications extend beyond environmental strain. These centres are not neutral utilities, but centralized hubs for computation, data storage, and increasingly, surveillance capacity. As Anwar explains, the shift toward cloud-based systems moves people away from ownership and into dependence.
The Illusion of Demand
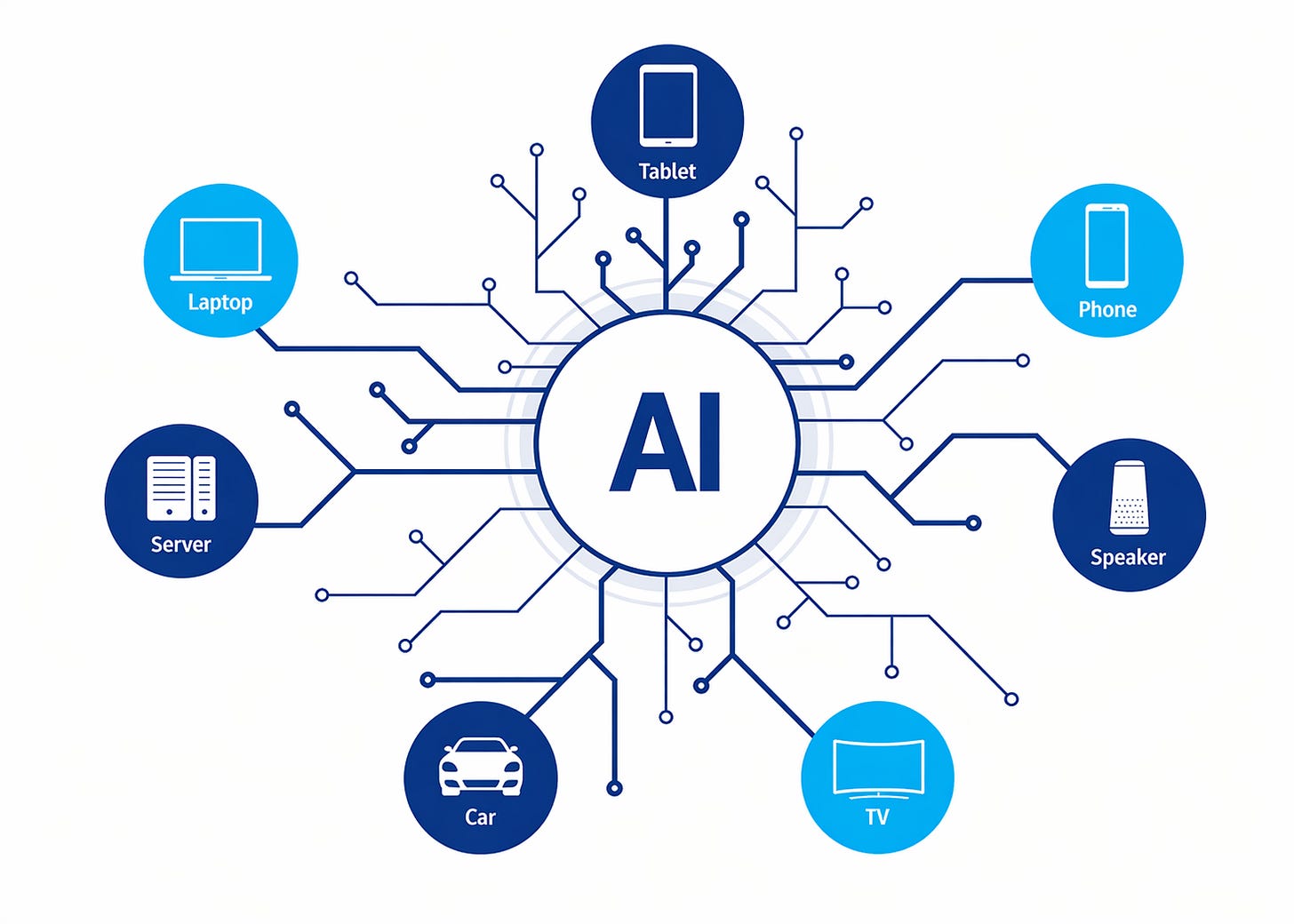
The rapid buildout of AI infrastructure is often framed as a response to growing demand. However, Anwar challenges this assumption, suggesting that demand is being actively manufactured. By embedding AI into devices, operating systems, and everyday tools, companies ensure consistent usage regardless of user intent.
This integration makes AI less of a choice and more of a default condition. He notes that users may not actively seek out AI, but they are increasingly unable to avoid it. The infrastructure requires engagement, and that engagement is engineered into the products people already rely on.
This creates a self-reinforcing cycle. Data centres expand to support AI, AI is embedded to justify those expansions, and users become dependent on systems they did not consciously adopt. Over time, this dynamic shifts not only behaviour, but also how individuals think, create, and make decisions.
The Danger of Digital ID
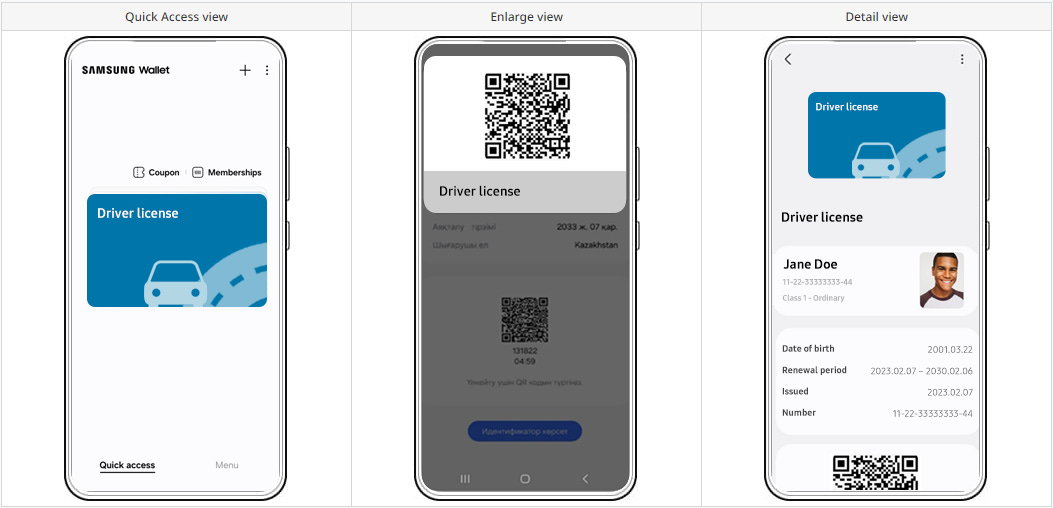
Alongside AI expansion, Anwar’s global digital ID report highlights the near-universal movement toward centralized identity systems. His analysis found that virtually every country is developing or implementing some form of digital ID, with only a handful of exceptions in remote or unstable regions.
Digital ID is at its most invasive when legal identity is combined with biometric data, such as facial recognition or fingerprint scans. Once these elements are linked, a persistent and verifiable identity is created that can be accessed across multiple systems.
This process is often less visible than expected. He points to financial institutions, insurance providers, and other intermediaries who are collecting biometric data in the name of convenience. Even if governments are not directly requesting information in a given moment, they may later consolidate these third party data collections into national systems.
From Identification to Control
The significance of digital ID becomes clearer when paired with surveillance technologies. Anwar draws a distinction between current facial recognition systems, which rely on probabilistic identification, and future systems tied to verified identity databases.
Without a confirmed link to legal identity, surveillance remains limited in its authority, since any facial recognition is subject to question. However, once the link is established, systems will have the power to enforce compliance, restrict access, or track individuals with far greater precision. This marks a shift from observation to control.
Anwar points to international examples, such as in Russia, where identity systems have already been leveraged in enforcement contexts. These developments suggest that the trajectory is not just speculative, but actively unfolding in multiple regions.
Surveillance Culture and Conditioning
Perhaps the most revealing development is not technological, but cultural. Anwar’s research into U.S. school systems shows how surveillance infrastructure expanded rapidly following the “pandemic,” when large funding programs provided schools with unprecedented resources. He notes that this sudden influx of funding created the conditions for rapid adoption, often without meaningful oversight or long-term consideration.
With this funding, schools deployed millions of devices, often equipped with monitoring software. Tools such as GoGuardian now permit administrators to observe student activity in real time, restrict access, and analyze behavior. Importantly, these systems often remain active outside school hours, extending surveillance into students’ homes.
He also highlights the emergence of behavioral tracking systems that categorize students based on language, emotional indicators, or perceived risk. Anwar references a group of technically skilled students who exposed vulnerabilities in these systems, demonstrating that sensitive monitoring databases could be accessed far more easily than expected.
Beyond the technical risks, the long-term effect is normalization, where constant monitoring becomes an accepted condition of daily life. Children who grow up under these systems will inevitably begin to internalize the idea that they are always being watched, not just in structured environments like classrooms, but in their private spaces as well. This can subtly reshape behavior, encouraging self-censorship, reducing spontaneity, and conditioning them to align with perceived expectations rather than explore freely. If this continues, the psychological boundary between public and private is likely to dissolve, and all resistance to authoritarianism will become nearly impossible.
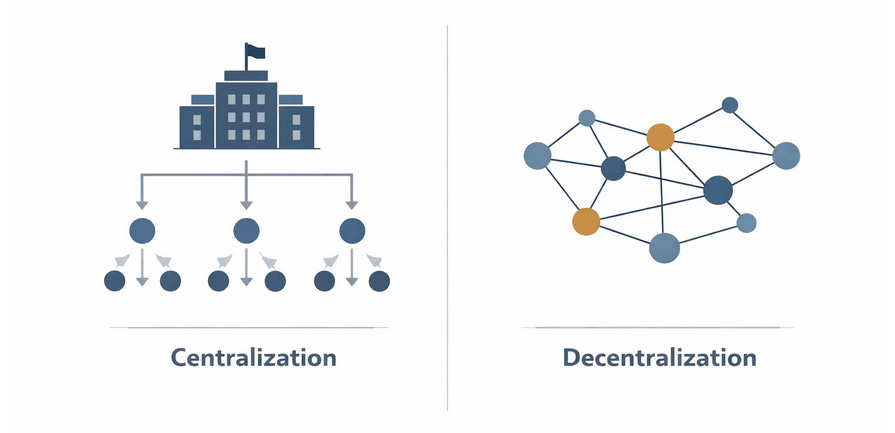
Centralization vs. Sovereignty
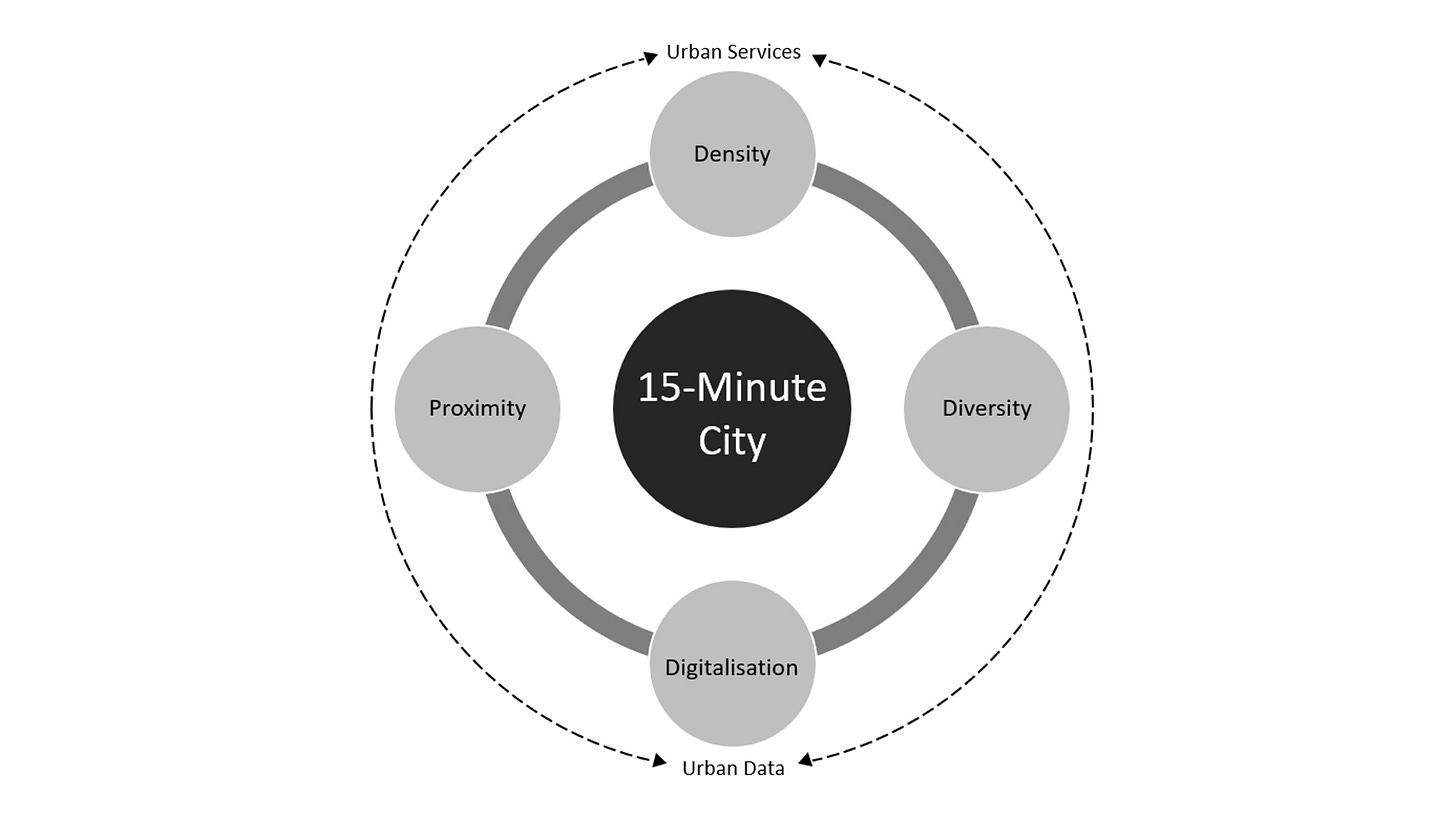
Across these domains, a clear tension emerges. On one side is centralization, represented by data centres, cloud computing, digital identity systems, and integrated surveillance. On the other is sovereignty, which involves the ability of individuals to control their own tools, data, and digital presence.
Rather than rejecting technology outright, Anwar advocates for alternative approaches. His company, Above Phone, with its privacy-focused devices and his educational platform Take Back our Tech are efforts to return control to the user. Local AI is another suggestion he makes to retain functionality without surrendering data to centralized systems.
The Role of Awareness and Noncompliance
Despite the scale of these developments, Anwar emphasizes that the outcome is not predetermined. Systems of control rely on widespread participation, and without it, their reach is limited. This places importance on individual and collective decision-making.
Noncompliance is a practical strategy. This includes refusing unnecessary biometric scans, seeking alternatives to centralized services, and questioning default technological integrations. While these actions may appear small, they introduce friction into systems designed to operate seamlessly.
Anwar also highlights the importance of local engagement. Through his data centre map, Anwar aims to connect individuals with community groups already addressing environmental and infrastructure concerns. In some cases, local activism has successfully halted major projects, demonstrating that intervention remains possible.
A Narrow Window to Reverse Course
The current moment is transitional. The systems described are not fully realized, but they are advancing rapidly and becoming more integrated into daily life. This creates a narrowing window in which meaningful choices can still influence the outcome.
Decisions made now, whether at the individual, community, or institutional level, will shape the balance between progress and control. Once systems are fully embedded, they become far more difficult to challenge or reverse. We must act quickly to ensure that our children inherit a free world with technology which serves them, rather than controlling them.
Additional Resources:
Data Centre Report. Above mapped over 3400 US data center locations, analyzed water stress, and shared solutions. Link↗
Digital ID Report. Above analyzed digital ID rollouts, mandates, and impacts, offering answers and solutions in a new report. Link↗
Sovereign AI Guide. How AI works, its costs and risks, and practical, privacy-focused use grounded in critical thinking. Link↗
Take Back Our Tech. A front-line public advocacy mission led by Hakeem, focused on reclaiming digital sovereignty: Link↗
Save up to $150 on private phones and laptops
Save up to $150 on privacy-focused devices—including laptops, tablets, and phones—while supporting the educational and advocacy work of my team, Take Back Our Tech, and Above. Use discount code DRTROZZI or access the offer through the link below.